Audit¶
The Audit module provides a suite of tools designed to investigate the network state, search through configurations, and monitor device behavior without altering the live environment.
Data gathering¶
Retrieve operational state data (non-configuration data) from your devices in real-time. Generate network-wide reports: MAC address tables, LLDP neighbors, 802.1x sessions, etc.
Data collection¶
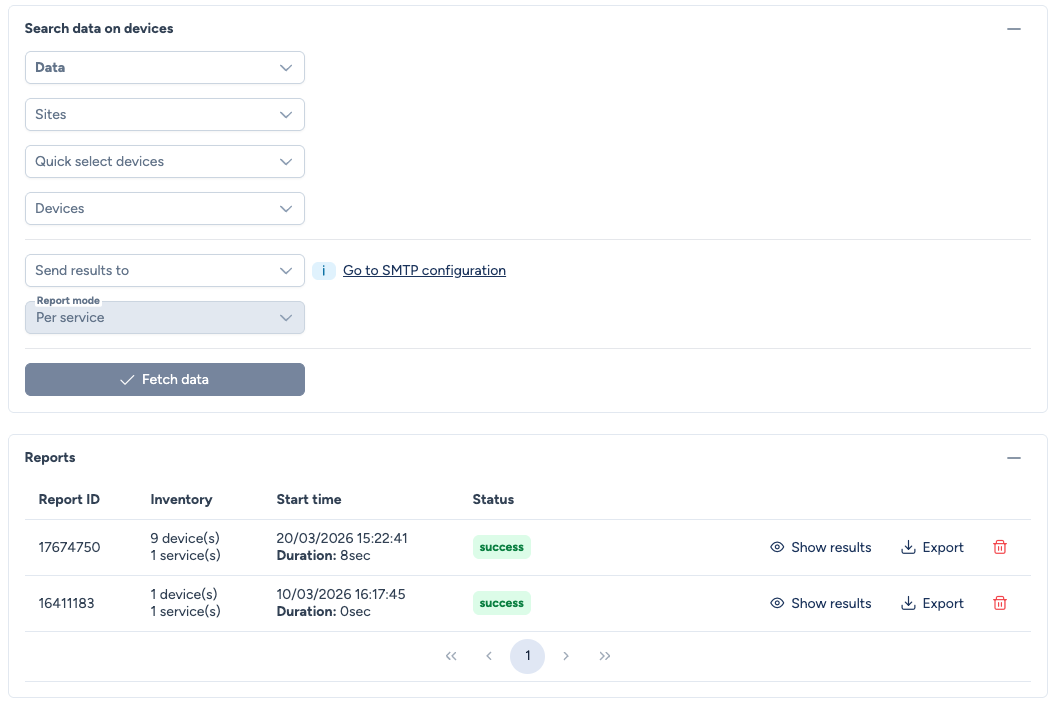
The collection form lets you configure your query:
- Data: Select one or more data types to collect (e.g.,
GetVLANsbyInterface,GetMACAddressTable,802.1x). - Sites: Select the sites to query.
- Quick select devices: Quick selection by device type.
- Devices: Fine-grained selection of individual devices.
- Send results to: (Optional) Select one or more recipients to receive the report by email. SMTP configuration must be done beforehand.
- Report mode: The report grouping mode (
Per serviceorPer device). - Fetch data: Launches the collection on the selected devices.
Reports¶
Each collection generates a report available in the Reports section. A report contains:
- Report ID: Unique report identifier.
- Inventory: Number of devices and services queried.
- Start time: Launch date and time, with execution duration.
- Status: Collection result (
success,error).
Available actions:
- Show results: Displays the detailed report results.
- Export: Downloads the data in CSV/Excel format.
- Delete: Removes the report from history.
Results visualization¶
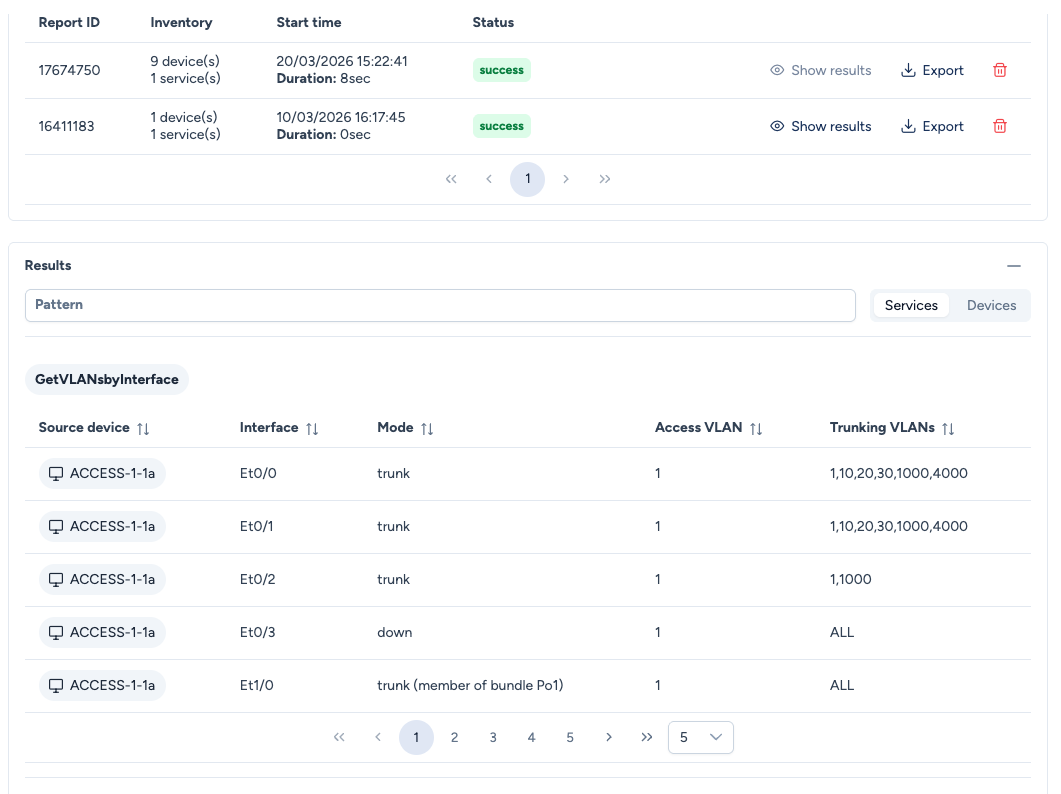
The Results section offers two perspectives to analyze the data. Toggle between them using the Services and Devices buttons:
- Services: Groups data by collection type. Ideal for global audits (e.g., "all VLAN interfaces across the entire site").
- Devices: Groups data by device. Ideal for targeted checks on a specific device.
A Pattern field lets you filter the displayed results.
802.1x specific columns¶
The 802.1x data gathering template includes additional columns for authentication session auditing:
- Switchport Mode: the port configuration mode (access, trunk, etc.).
- Data VLAN Conf: the data VLAN configured on the port.
- Voice VLAN Conf: the voice VLAN configured on the port.
- Auth Fail: the fallback VLAN applied when authentication fails.
- No Response: the fallback VLAN applied when no supplicant responds.
Explore configurations¶
Search for specific configuration lines across hundreds of backup files without opening them individually.
Usage¶
- Pattern: Enter a text string or Regex (e.g.,
telnet,password 7,192.168.1.1). - Scope: Select the sites or device types to search.
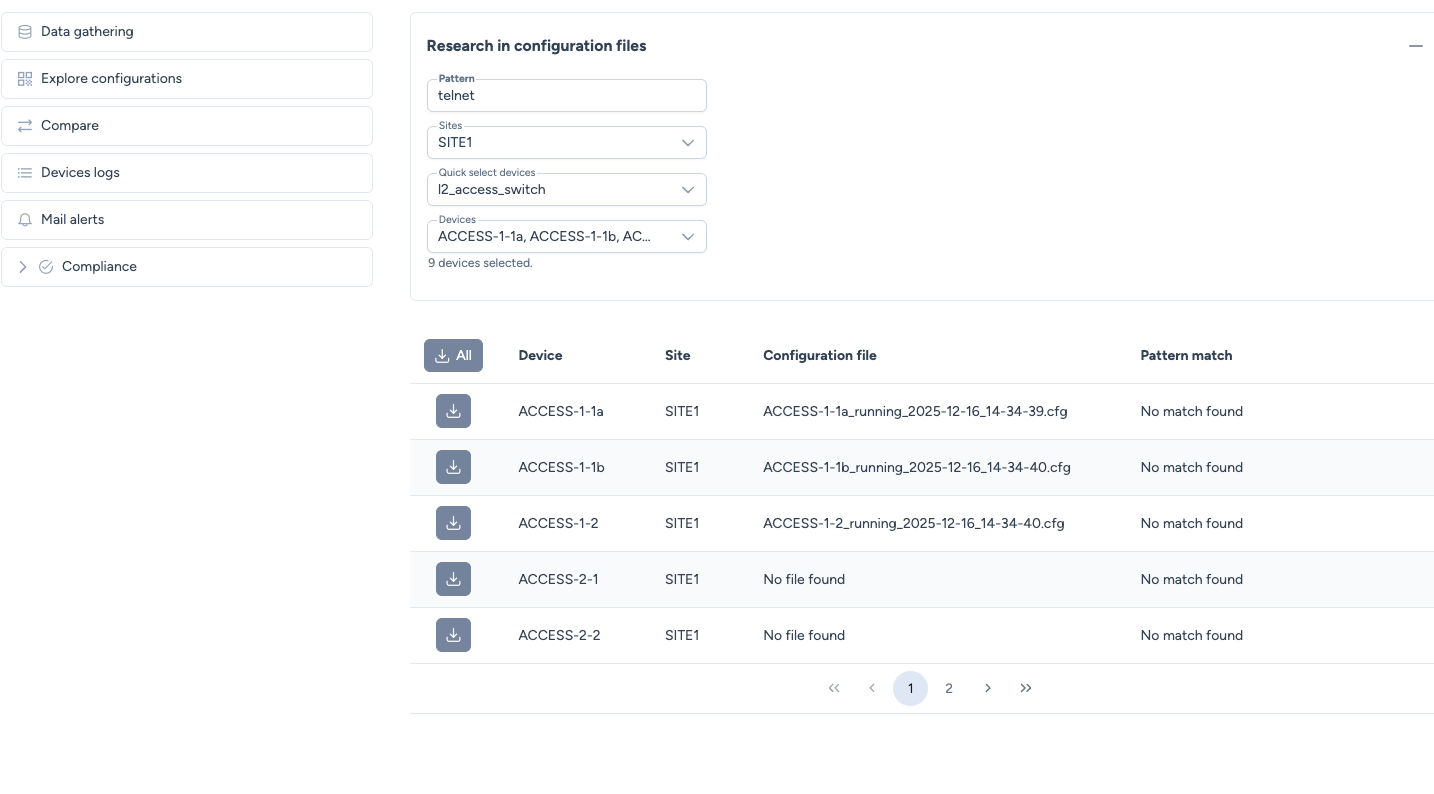
Results¶
The table displays the match status for each device.
- Pattern match: Shows whether the string was found.
- Download: You can download the specific configuration file directly from this view.
Compare configurations¶
The Compare tool provides a visual "Diff" between two configuration files.
Usage¶
- Change Validation: Compare the
running-configof a device at two different dates (e.g., "Before" vs "After" maintenance). - Standardization: Compare the configurations of two similar devices (e.g.,
ACCESS-1-1avsACCESS-1-1b).
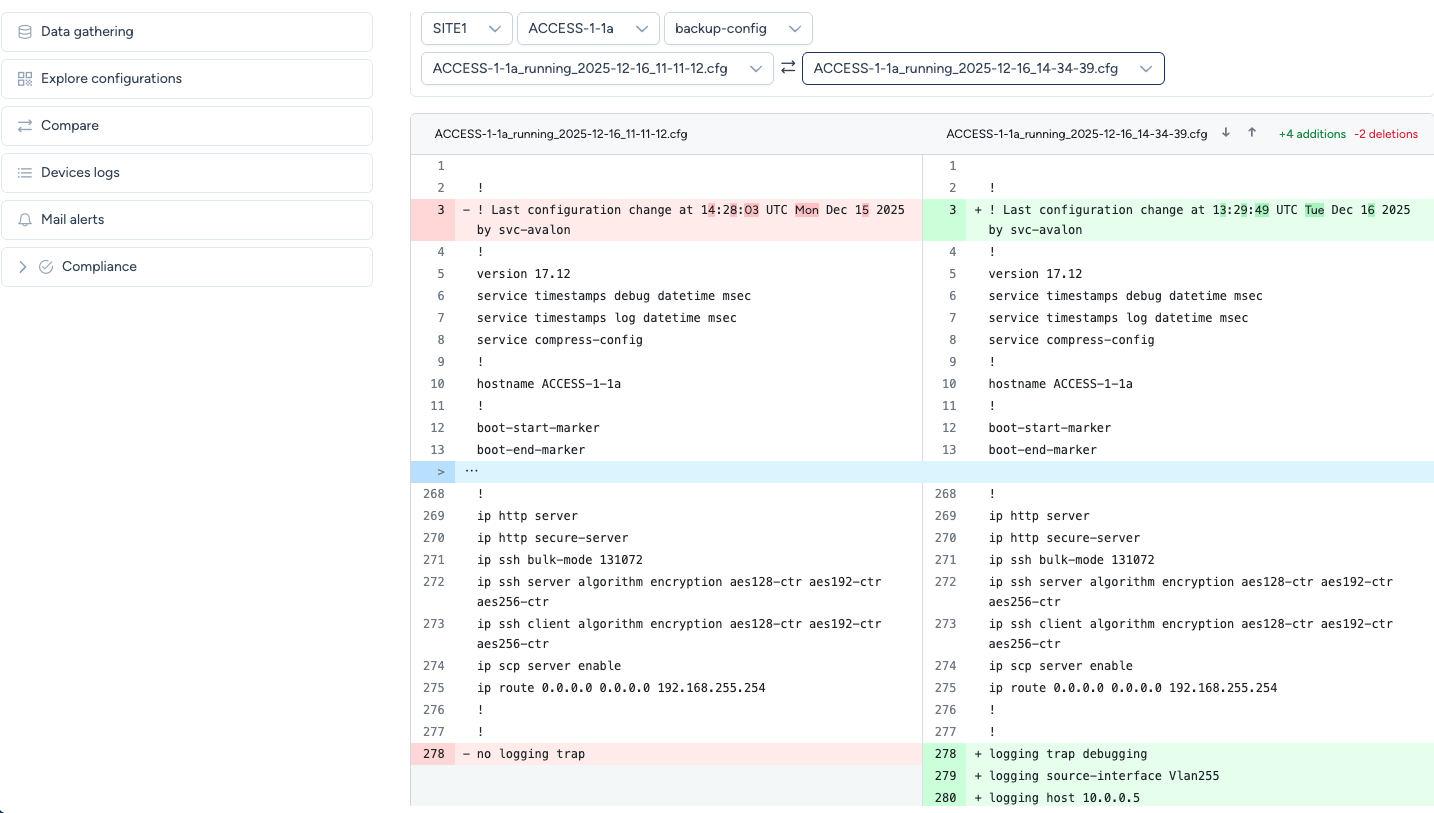
Visual indicators¶
- Green Lines present in the right file but missing in the left (Additions).
- Red Lines present in the left file but missing in the right (Deletions).
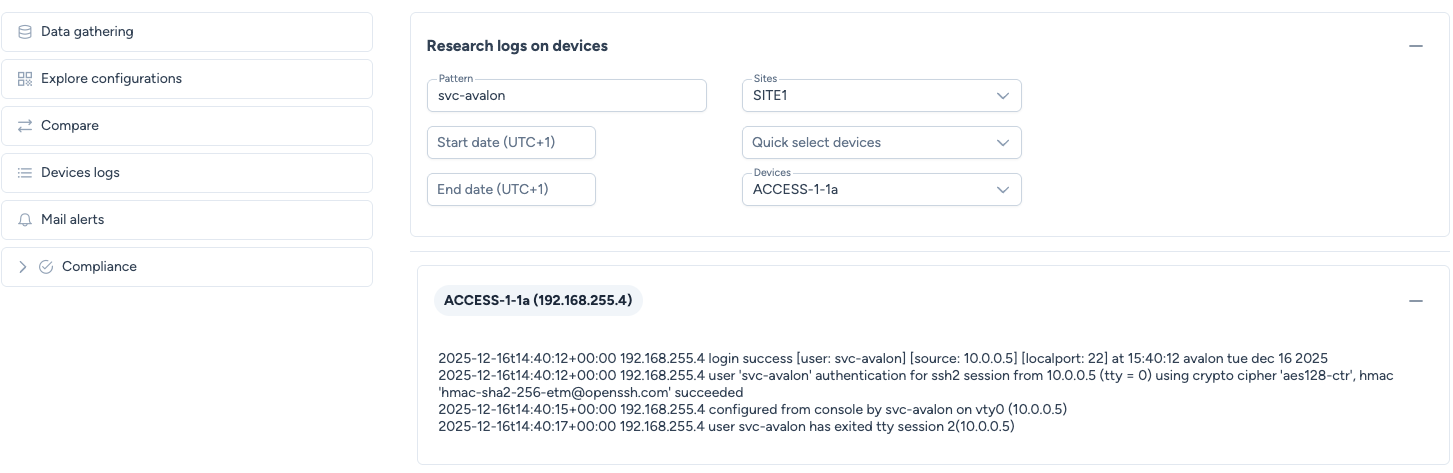
Devices logs¶
This section provides a centralized interface to search through Syslog messages exported by devices to Avalon.
Usage¶
You can narrow down the search using:
- Pattern: Keyword search (e.g.,
link-flap,OSPF,user-login). - Time Window: Start date and End date.
- Scope: Specific Sites or Devices.
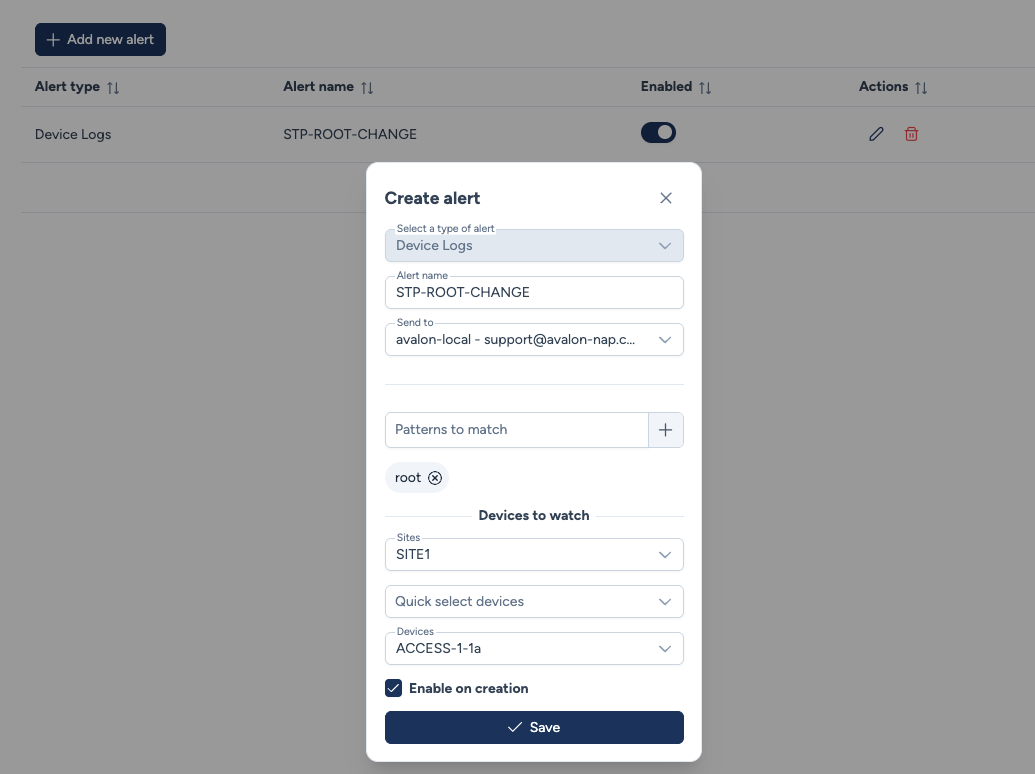
Mail alerts¶
While Devices logs is for historical investigation, Mail alerts allows for proactive monitoring. You can configure Avalon to send an email notification immediately when a specific log pattern is detected.
Creating an alert¶
- Alert Type: Currently supports
Device Logs. - Alert name: A descriptive name for the alert.
- Recipient / Send to: Select the email address to notify.
- Pattern: The Regex or string to watch for (e.g.,
root,fan fail). - Devices to watch: Define which devices to monitor.
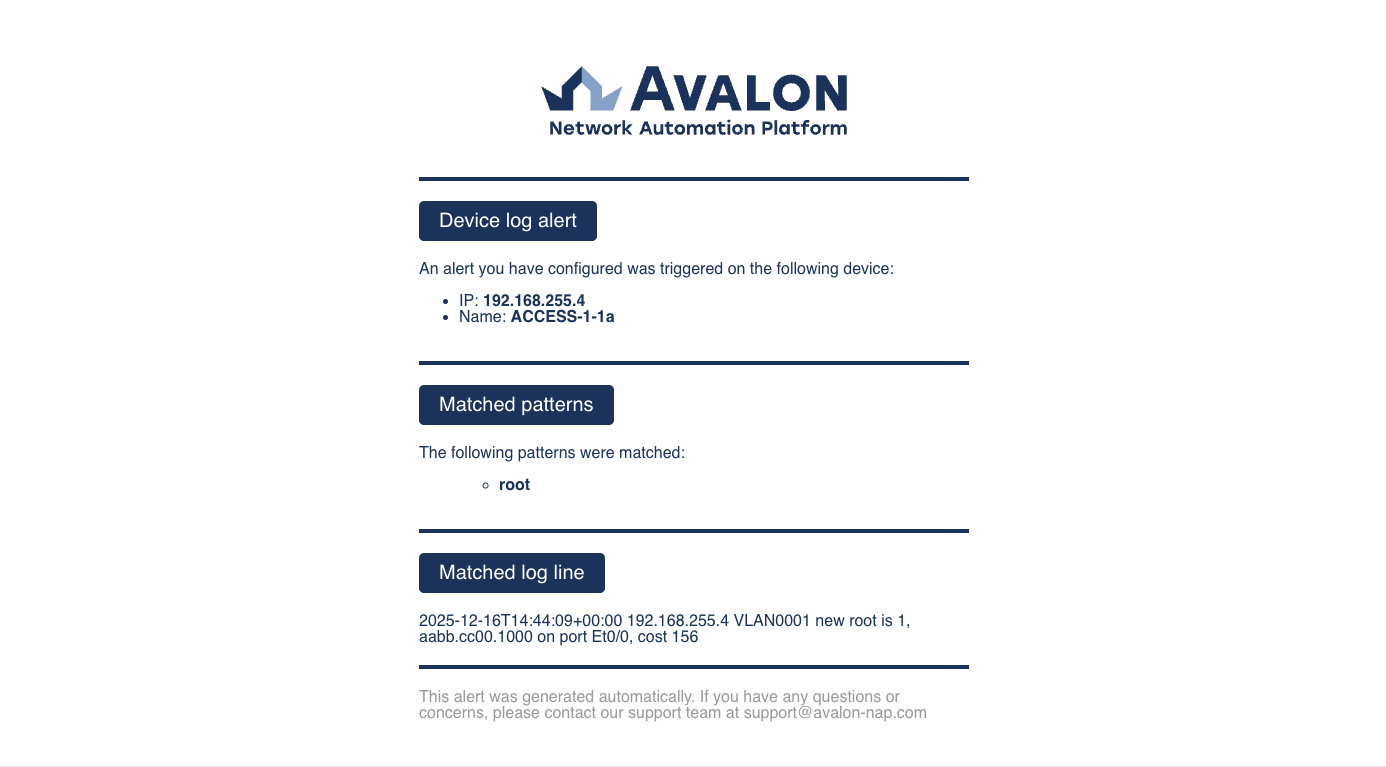
Email example¶
When triggered, the email provides the context required for troubleshooting: the Device IP, the matched pattern, and the raw log line.
Compliance¶
The Compliance view checks the consistency of device operational states.
Usage¶
Currently Avalon supports VLAN Mismatches on trunk links.
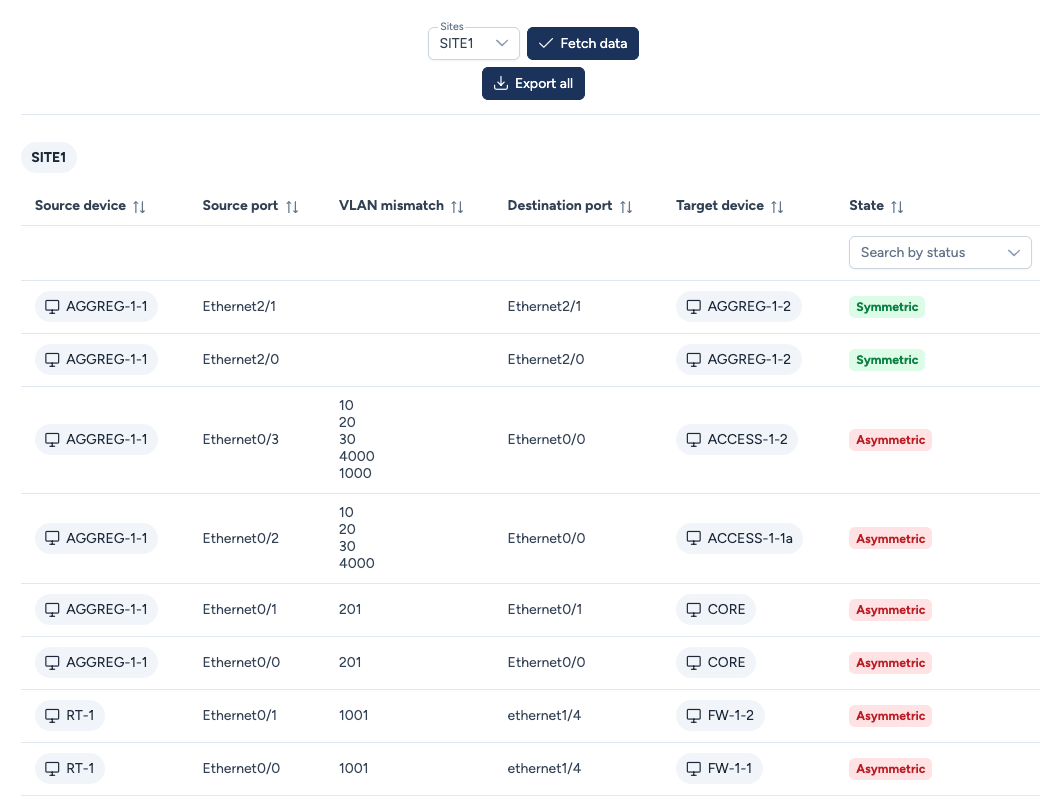
Column details¶
- Source/Destination: The two endpoints of the link.
- VLAN Mismatch: Lists VLANs that are allowed on one side but missing on the other.
- State:
- Symmetric The configuration matches on both sides.
- Asymmetric A configuration mismatch was detected (e.g., VLAN 10 missing on one end).